Mar 31, 2026
BlogRBAC vs ABAC Comparison: Choosing the Right Access Control Model for Your Business
Your access control model determines whether you’ll pass your next compliance audit or face regulatory penalties that could cripple your growing business.
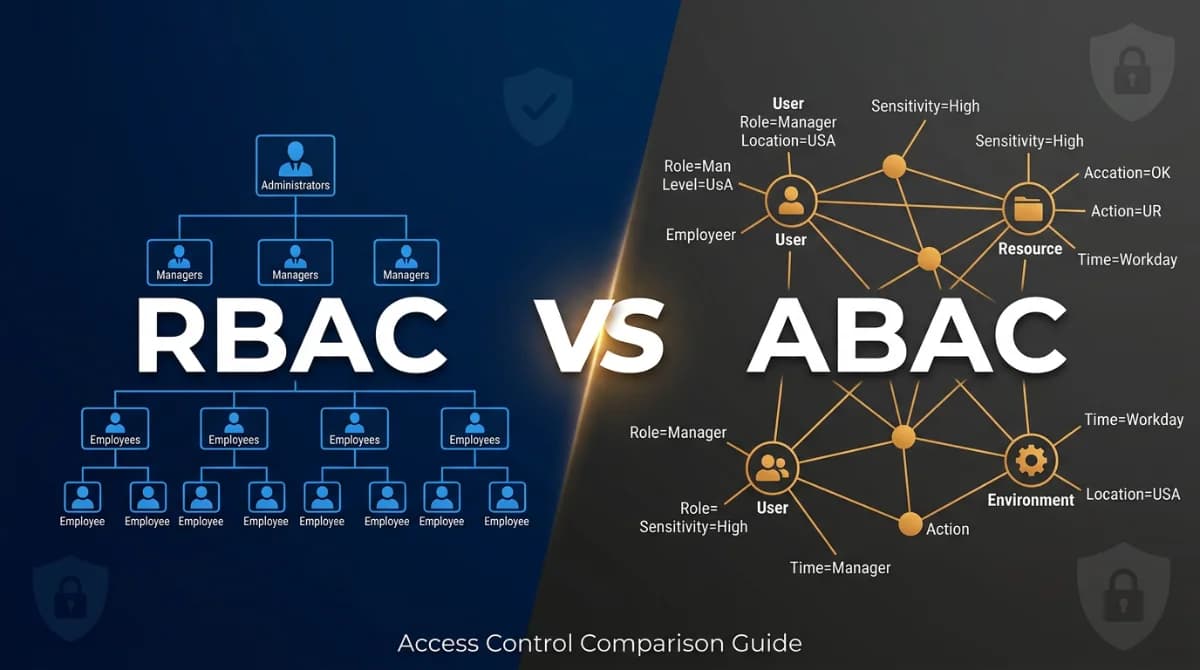
The rbac vs abac comparison reveals fundamental differences in how businesses control system access: RBAC assigns permissions based on job roles, making it simple but rigid; ABAC uses dynamic attributes for granular control but requires more complexity; while rule-based systems offer conditional logic between these extremes. For compliance officers managing audit readiness and risk exposure, choosing the right model means balancing simplicity with the flexibility needed for modern regulatory requirements.
This guide breaks down each access control model’s strengths and limitations, helping you select the approach that aligns with your compliance obligations while enabling secure business growth.
Understanding Access Control Models: The Foundation of Business Security
Access control models form the backbone of your organization’s data protection strategy and directly impact your ability to demonstrate compliance during audits. Every unauthorized access attempt, every over-privileged account, and every untracked permission change becomes a potential compliance violation waiting to surface during your next regulatory review.
Modern businesses face a critical challenge: maintaining audit-ready documentation while enabling the agility needed for growth. Your choice of access control entry determines:
• Audit trail clarity - How easily you can prove who accessed what and when
• Risk visibility - Your ability to identify and prevent compliance violations before they occur
• Regulatory alignment - How well your access controls map to specific compliance requirements
• Scalability burden - Whether growth creates exponential complexity or manageable expansion
• Evidence generation - The quality of documentation available for compliance assessments
The right access control model transforms security from a business inhibitor into a competitive advantage, enabling faster partner onboarding, smoother audit processes, and demonstrable risk management that builds stakeholder confidence.
What is RBAC (Role-Based Access Control)?
Role-Based Access Control, as formalized in 1992 by David Ferraiolo and Rick Kuhn, has become the predominant model for advanced access control because it reduces the complexity and cost of security administration in large networked applications. When an employee joins as a Finance Manager, they automatically receive all permissions associated with that role – access to accounting systems, financial reports, and payment platforms – based on the NIST RBAC standard (ANSI/INCITS 359-2004).
RBAC’s widespread adoption stems from its intuitive alignment with organizational structures:
• Predictable permission sets - Each role has clearly defined access boundaries
• Simplified administration - Add users to roles rather than managing individual permissions
• Clear audit trails - Reviewers easily understand why someone has specific access
• Established compliance mapping - Most regulatory frameworks recognize role-based structures
• Reduced training requirements - IT teams quickly grasp the role-permission relationship
However, RBAC’s simplicity becomes a liability as your business evolves beyond traditional hierarchies.
When RBAC Works Best for Your Business
RBAC excels in environments with stable organizational structures and predictable access patterns. Manufacturing companies with clear departmental boundaries, traditional banks with established hierarchies, and government contractors with rigid compliance requirements often find RBAC sufficient.
Key indicators that RBAC fits your needs:
• Static team structures - Employees rarely change departments or responsibilities
• Clear role definitions - Job functions have minimal overlap or ambiguity
• Limited external access - Few contractors, partners, or temporary workers
• Straightforward compliance - Regulations require basic role-based segregation
• Predictable growth - Expansion follows established organizational patterns
RBAC Limitations in Modern Business Environments
Growing businesses quickly discover RBAC’s breaking points. A Dubai-based fintech startup might start with five roles but find themselves managing fifty within a year as employees wear multiple hats and responsibilities blur across teams.
Role explosion occurs when an RBAC model accumulates so many roles that the access structure becomes unmanageable. Every unique access requirement generates a new role, leading to role explosion. When an organization has more roles than people, security teams can no longer confidently answer the question “who has access to what.”
Critical RBAC challenges include:
• Role explosion - Creating new roles for every unique permission combination
• Permission creep - Accumulating unnecessary access as employees change positions
• Cross-functional blindness - Inability to handle project-based or temporary access
• Compliance gaps - Difficulty proving least privilege access when roles grant broad access
• Revocation delays - Complex role changes when employees leave or transfer
What is ABAC (Attribute-Based Access Control)?
ABAC is a logical access control methodology where authorization to perform a set of operations is determined by evaluating attributes associated with the subject, object, requested operations, and, in some cases, environment conditions against policy, rules, or relationships that describe the allowable operations for a given set of attributes. Instead of asking “What role does this person have?”, ABAC asks “Do this person’s current attributes satisfy the policy requirements?”
Per NIST SP 800-162, ABAC’s policy-driven architecture enables:
• Contextual decisions - Access varies based on location, time, device security status
• Granular control - Policies can consider dozens of attributes simultaneously
• Dynamic adaptation - Access rights change automatically as attributes update
• External user support - No pre-provisioning required for partners or contractors
• Regulatory precision - Fine-grained controls align with specific compliance requirements
ABAC Implementation Complexity
While ABAC offers superior flexibility, implementation requires significant upfront investment. Organizations must define attribute schemas, establish policy languages, and integrate multiple data sources to provide real-time attribute evaluation.
Common ABAC implementation challenges:
• Attribute management - Maintaining accurate, current attributes across systems
• Policy complexity - Writing and testing complex conditional logic
• Performance impact - Real-time attribute evaluation can slow access decisions
• Integration overhead - Connecting disparate systems for attribute collection
• Debugging difficulty - Troubleshooting access denials across multiple attribute sources
What is Rule-Based Access Control?
Rule-based access control systems evaluate conditional statements to grant or deny access, offering more flexibility than RBAC while maintaining simpler implementation than full ABAC. These systems excel when access decisions depend on specific conditions like time windows, location restrictions, or data classification levels.
Rule-based systems work well for:
• Time-sensitive access - Restricting system access to business hours
• Location-based controls - Blocking access from unauthorized geographic regions
• Data classification enforcement - Applying different rules based on information sensitivity
• Conditional workflows - Requiring additional approvals for high-risk operations
• Temporary access grants - Automatically expiring permissions after specified periods
RBAC vs ABAC vs Rule-Based: Complete Comparison
Feature | RBAC | ABAC | Rule-Based |
|---|---|---|---|
Implementation Complexity | Low | High | Medium |
Administrative Overhead | Medium | High | Low |
Scalability | Poor (role explosion) | Excellent | Good |
Granular Control | Limited | Excellent | Good |
Compliance Alignment | Good | Excellent | Good |
External User Support | Poor | Excellent | Medium |
Performance Impact | Low | Medium | Low |
Audit Trail Quality | Good | Excellent | Good |
Policy Flexibility | Low | Excellent | Medium |
Integration Complexity | Low | High | Medium |
Best For | Stable organizations | Dynamic environments | Conditional access |
How to Choose the Right Access Control Model for Your Organization
Selecting the optimal access control model requires evaluating your organization’s current state and future trajectory:
Choose RBAC if:
- Your organizational structure is stable with clearly defined roles
- You have limited IT resources for complex system management
- Compliance requirements focus on basic role segregation
- Most users have standard, predictable access needs
Choose ABAC if:
- Your business operates in dynamic, rapidly changing environments
- You need fine-grained control over sensitive data and resources
- Compliance demands detailed audit trails and contextual access decisions
- You regularly work with external partners and contractors
Choose Rule-Based if:
- You need conditional access beyond basic roles
- Time, location, or device-based restrictions are critical
- You want more flexibility than RBAC without ABAC’s complexity
- Your access patterns follow predictable conditional logic
How ShieldNet Access Simplifies Access Control Implementation
ShieldNet Access eliminates the complexity of choosing between access control models by providing identity-based verification that works with your existing systems. Instead of managing roles or complex attribute policies, ShieldNet Access verifies every connection attempt against your organization’s identity directory.
Key advantages for growing SMEs:
• No role management - Access decisions based on verified identity and device status
• Automatic compliance logging - Every access attempt generates audit-ready documentation
• Seamless integration - Works with Microsoft 365, Google Workspace, and cloud applications
• Zero installation - Cloud-based deployment without infrastructure changes
• Continuous verification - Real-time identity and device validation for every connection
This approach gives you the security benefits of advanced access control without the administrative complexity, making it ideal for businesses that need enterprise-grade protection without enterprise-scale IT teams.
Frequently Asked Questions: RBAC vs ABAC Access Control
What is the main difference between RBAC and ABAC?
RBAC assigns permissions based on predefined job roles, while ABAC evaluates multiple attributes (user, resource, environment, action) in real-time to make access decisions. RBAC asks “What role does this user have?” while ABAC asks “Do this user’s attributes meet the policy requirements?”
Which access control model is better for compliance?
ABAC generally provides better compliance support due to its granular control and detailed audit trails. However, RBAC can be sufficient for organizations with straightforward compliance requirements and stable role structures. The choice depends on your specific regulatory obligations and organizational complexity.
How do I know if my organization has role explosion?
Signs of role explosion include: having more roles than employees, creating user-specific roles, difficulty explaining what each role does, and spending more time managing roles than users. If your IT team struggles to answer “who has access to what,” you likely have role explosion.
Can RBAC and ABAC be used together?
Yes, hybrid approaches are common. Organizations often use RBAC for basic access control and ABAC for fine-grained permissions on sensitive resources. This provides the simplicity of roles for routine access while enabling attribute-based decisions for critical systems.
What are the costs of implementing ABAC vs RBAC?
RBAC typically has lower upfront costs but may become expensive due to role explosion and administrative overhead. ABAC requires higher initial investment in policy development and system integration but often reduces long-term administrative costs through automation and better scalability.
How does rule-based access control compare to RBAC and ABAC?
Rule-based access control sits between RBAC and ABAC in terms of complexity and capability. It’s more flexible than RBAC for conditional access scenarios but simpler to implement than full ABAC. It works well for time-based restrictions, location controls, and data classification enforcement.
Related Articles

May 12, 2026
ShieldNet 360 at Biztech 2026: Security Made Simple in the AI era
Today, on May 12, 2026 in Ho Chi Minh City, ShieldNet 360 is attending Biztech 2026 and speaking in the session Cyber Security in the AI Era with the topic “Security Made Simple for SMEs in the AI Era”, delivered by Mr. Tung Nguyen (Ethan), Director of ShieldNet 360.

May 5, 2026
ShieldNet Defense: AI-powered threat detection for SMEs
Discover ShieldNet Defense, an AI-powered threat detection platform that explains risks in plain language and helps SMEs detect, analyze, and respond to threats faster.

May 4, 2026
AI threat detection demo: detect, analyze, respond
Learn how an AI threat detection demo works with a clear detect–analyze–respond workflow. See dashboard outputs, real scenarios, and how SMEs stop threats in minutes.

Protect your business with ShieldNet 360
Get started and learn how ShieldNet 360 can support your business.